Cyber Mythbusters: Debunking One Myth at a Time
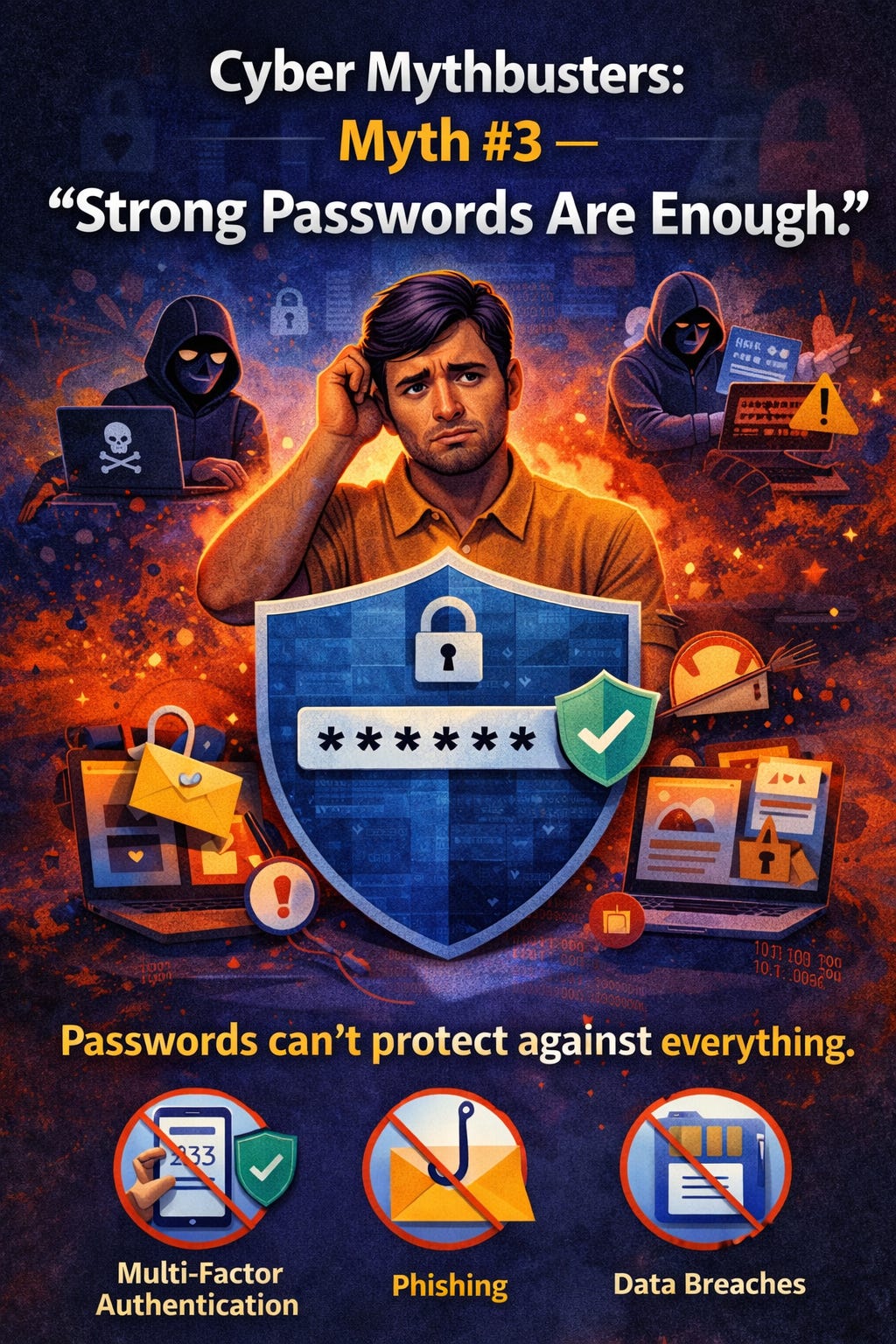
Myth #3 — “Strong Passwords Are Enough.”
Myth #3 — “Strong Passwords Are Enough.
Let’s be honest for a second: most of us think we’re doing the right thing when we use a “strong password.” Something like Winter2024!, GalaxyHorse19$, or the classic P@ssw0rd123! that every tech blog said was “secure” back in 2013.
So the myth goes like this:
“If my password is strong, I’m safe.”
It sounds right. It feels right.
Unfortunately, it’s outdated — and attackers know it.
Let’s break down why strong passwords alone don’t cut it anymore and what the data says about it.
The Myth
People assume that if their password:
Has a capital letter
Has a number
Has a symbol
Is longer than eight characters
…then it’s automatically secure.
The problem? Attackers don’t break in the way they used to.
Reality: Passwords Are Failing at Scale
1. Most people still reuse passwords — which makes “strong” meaningless
A 2025 study of 19 billion leaked passwords found that 94% were reused or weak, and only 6% were unique.
That means if you reuse any password — even a “strong” one — it becomes worthless the moment it leaks from any site. [cybernews.com]
And attackers don’t try logging in manually. They feed those leaked passwords into automated tools.
2. Password cracking tools have gotten ridiculously fast
According to password security research in 2025, seven of the ten most common passwords can be cracked in under one second, and many “complex” patterns like P@ssw0rd or Welcome@123 appear frequently in breach dumps and get cracked near-instantly too. [deepstrike.io]
Even more concerning: modern GPU clusters can brute-force an 8‑character password (lowercase only) in about three weeks, and fully complex 8‑character passwords in months, thanks to massive leaps in hardware power and attacker tooling. [deepstrike.io]
Your “strong” password from a few years ago? Today it’s a warm-up exercise.
3. Credential stuffing is now industrial-scale
Here’s where the real-world danger comes in.
In 2025:
Credential stuffing made up 22% of all breaches, more than any other initial access method, including phishing. [deepstrike.io]
Attackers used automation to launch billions of login attempts using stolen username/password pairs from old breaches.
Many industries saw 20–25% of all login traffic being malicious automated attempts, not real users. [deepstrike.io]
Translation:
Attackers don’t need to “crack” your password at all — they just reuse it.
If you’ve used your strong password more than once, it’s already compromised.
4. Info-stealer malware bypasses passwords entirely
In 2024 alone, infostealer malware like RedLine and Raccoon stole 548 million passwords and 17 billion session cookies from infected devices. [deepstrike.io]
Session cookies are the real danger:
Attackers can often use them to log in without needing your password or MFA.
Meaning:
You can have the strongest password in the world — and attackers can walk right past it.
Real-World Example: The “Strong Password” That Wasn’t
A major 2025 breach involved a company where employees followed “corporate password rules.”
They used long, complex passwords with numbers, symbols, and uppercase letters.
Still, attackers got in.
Why?
One employee reused their complex password on a personal site years earlier.
That site was later breached.
Attackers grabbed the leaked password.
They used automated bots to test it on corporate accounts.
It worked.
The company didn’t have MFA on that service.
Attackers stayed inside the network for 292 days, undetected, because credential-based attacks take the longest to discover. [deepstrike.io]
Strong password? Yes.
Secure account? Not even close.
So what does make passwords safe today?
1. Unique passwords
Reusing one password — even a “perfect” one — is the fastest way to get compromised.
84% of people still reuse passwords across platforms in 2025, and attackers depend on that behavior. [demandsage.com]
2. Multi-Factor Authentication (MFA)
Passwords are something you know.
MFA adds something you have.
MFA blocks most automated attacks.
It isn’t perfect, but it dramatically raises the cost for attackers.
3. Passphrases instead of complex character soup
“GreenCoffeeHorseSkyline” beats “W1nter2024!” every time.
Longer is better than “complex but short.”
4. Monitoring for leaked credentials
With billions of credentials leaked yearly, checking if your passwords appear in dumps is essential.
Why Passkeys Are the Future
Google reports 400+ million accounts now using passkeys, which cannot be phished or reused, making them resistant to the very attacks dominating 2025 and 2026. [deepstrike.io]
Passkeys eliminate weak links like:
Password reuse
Guessability
Phishing
Brute forcing
Credential stuffing
They aren’t perfect yet, but they’re a major improvement.
Final Takeaway
Strong passwords used to be enough.
Today, the data says otherwise:
94% of leaked passwords are reused or weak [cybernews.com]
22% of breaches start with stolen credentials, the largest single vector in 2025 [deepstrike.io]
Attackers stole 548 million passwords via infostealer malware in one year [deepstrike.io]
Password cracking hardware continues to accelerate faster than most users can adapt [deepstrike.io]
A “strong password” is no longer a shield.
Security now comes from:
Unique passwords
MFA
Passphrases
Passkeys
Reducing reuse
Staying aware of breaches
A password is just one layer — and it can’t carry the whole load anymore.
If you’re finding Cyber Mythbusters helpful, consider subscribing and sharing this with someone who still thinks their passwords are “good enough.” Your support helps Netizen Watch keep digital security simple, real, and accessible.
Next Week on Cyber Mythbusters
Myth #4 — “My Phone Is Safe By Default.”
We’ll explore why the device most people trust the most is quietly becoming attackers’ favorite target.