Loops, Cycles, and Survival: What Fighter Pilots, Motorcycle Riders, and Incident Responders All Have in Common
The Decision Frameworks That Keep You Alive — On the Highway, In the Cockpit, and Behind the Keyboard
Some of you reading this ride motorcycles. Some of you work in SOCs staring at dashboards all day. A few of you might have done both while also serving in the military. Regardless of where you sit, I want you to understand something that changed the way I think about cybersecurity, riding, and honestly life in general: the best survival frameworks in the world all say the same thing.
They just use different words.
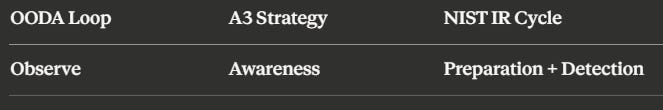
Today we’re going to break down three frameworks that operate on the same underlying principle — continuous, looping decision-making under pressure. They come from three completely different worlds, but when you lay them side by side the similarities are impossible to ignore. If you understand one of them deeply, you already understand the bones of the other two.
Let’s get into it. 🔥
The Three Frameworks
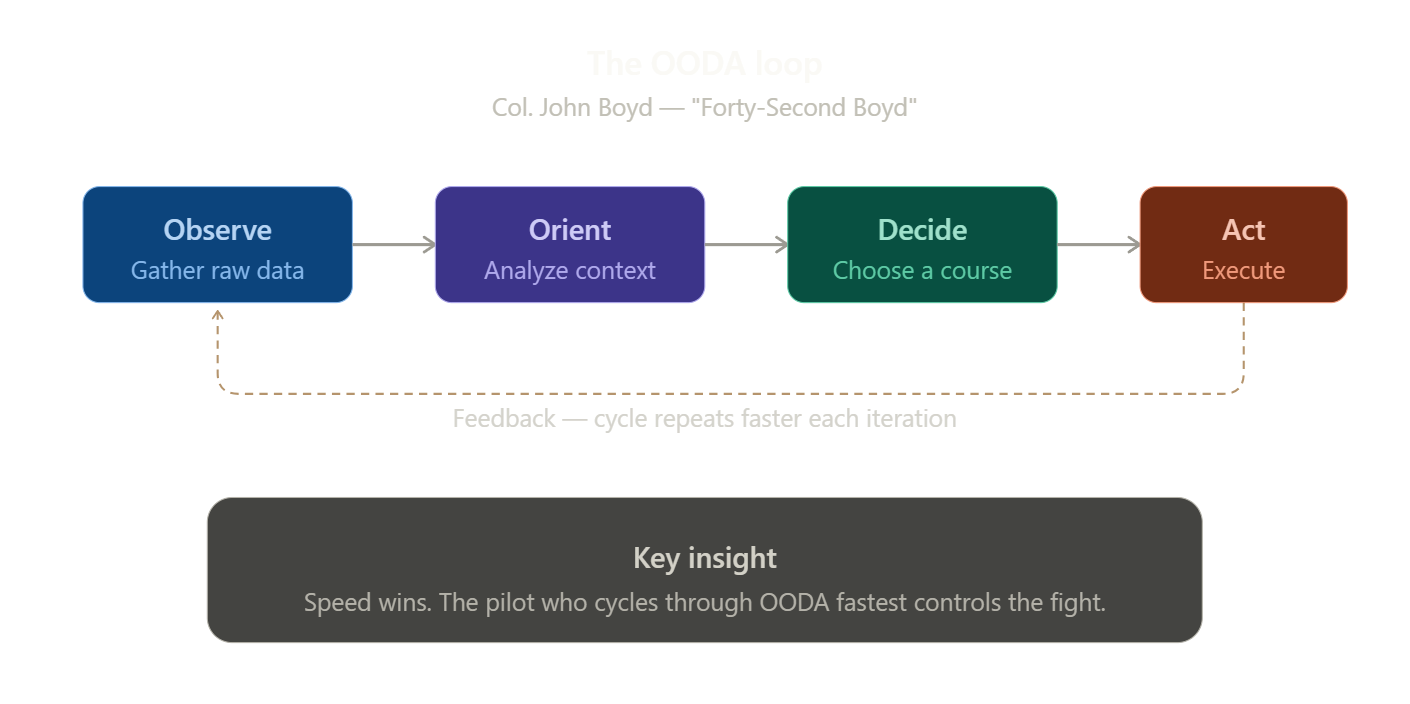
1. The OODA Loop — Observe, Orient, Decide, Act
Developed by U.S. Air Force Colonel John Boyd. The man earned the nickname “Forty-Second Boyd” because he could defeat any opposing pilot in simulated combat in under 40 seconds. He studied how fighter pilots won dogfights and distilled it into a framework that has since been adopted by the military, business strategists, and cybersecurity professionals worldwide.
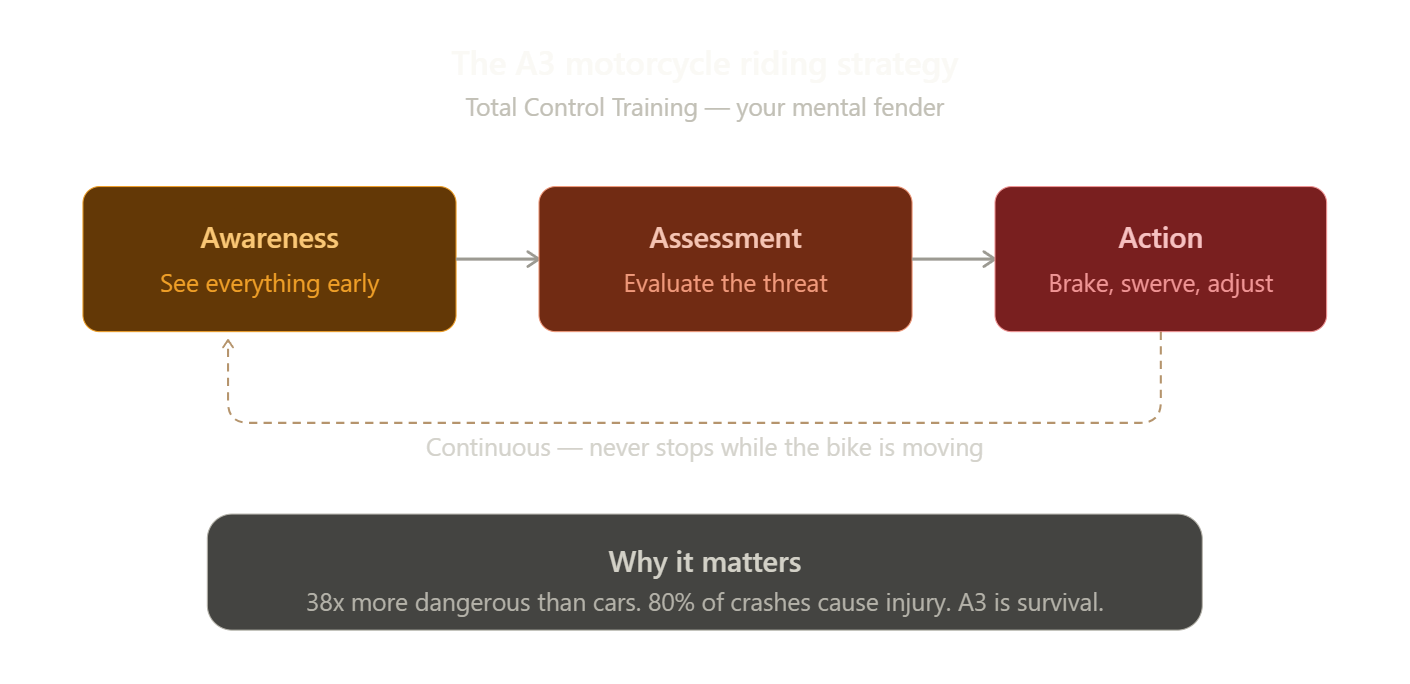
2. The A3 Motorcycle Riding Strategy — Awareness, Assessment, Action
Taught in motorcycle safety courses across the country through programs like the Total Control Training curriculum. This is the mental framework that keeps riders alive on machines that are 38 times more dangerous than cars. Eighty percent of motorcycle crashes result in rider injury. There is no fender to protect you. The A3 strategy is your fender.
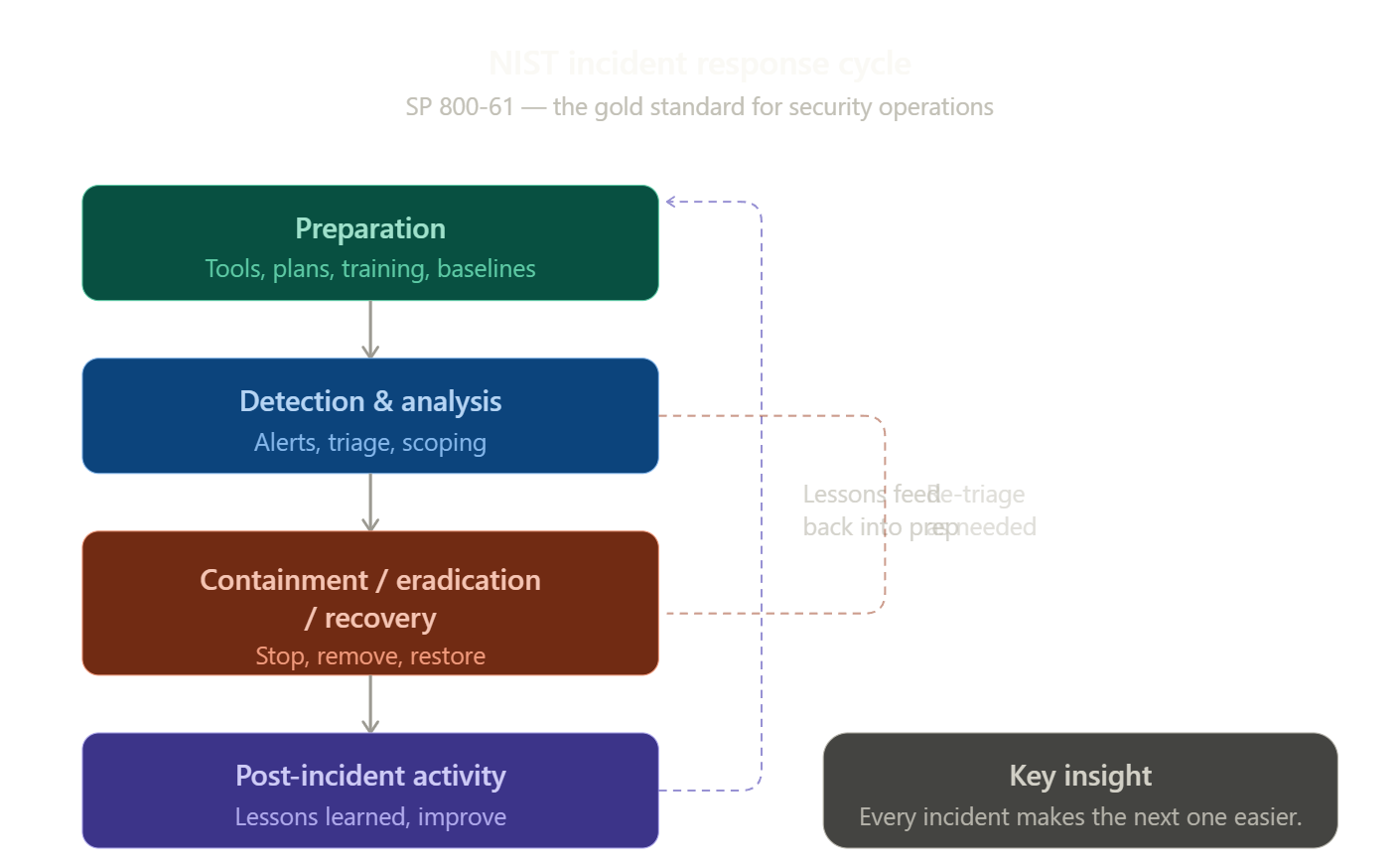
3. The NIST Incident Response Cycle — Preparation, Detection & Analysis, Containment/Eradication/Recovery, Post-Incident Activity
Defined in NIST SP 800-61 and widely considered the gold standard for how organizations should handle cybersecurity incidents. If you work in a SOC, an MSSP, or any security team worth its salt, this cycle is supposed to be the rhythm of your operation.
They’re All Loops. That’s the Point.
The first thing to understand is that none of these are checklists. They are loops. Cycles. They repeat. The output of the last step feeds directly back into the first step, and every rotation through the loop makes you sharper than the last one.
Colonel Boyd didn’t call it the OODA Process. He called it the OODA Loop. Why? Because in a dogfight the situation changes every fraction of a second. You observe, you orient yourself to what’s happening, you decide on a course of action, you act — and then you observe again because your action just changed the entire situation. The pilot who can cycle through this loop faster than the opponent wins. Period.
The A3 strategy works the same way on the road. You’re riding and you become aware of a car drifting into your lane. You assess the threat — is the driver distracted? Is there an escape route to the right? You take action — you adjust speed, change lane position, or prepare to brake. And then what? You’re right back to awareness because the road just changed. Maybe that car corrected. Maybe a new hazard appeared. The loop never stops until the engine does.
And the NIST Incident Response Cycle? Same energy. You prepare. You detect and analyze a threat. You contain it, eradicate it, recover. Then you conduct post-incident review — and that review feeds lessons learned directly back into preparation. The cycle starts over. Every incident you survive makes the next response better.
Three different worlds. One universal truth: survival belongs to the ones who loop fastest and learn deepest
Breaking Down the Parallels
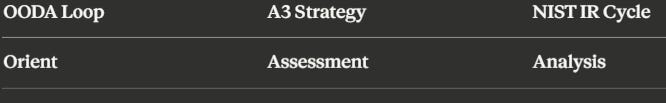
Let me map this out so you can see how tight the alignment really is.
Step 1 — Take In Your Environment
Boyd said the first step is gathering information from every available source. Not just what’s in front of you, but the full picture — your instruments, your peripheral vision, radio chatter, the behavior of the enemy.
On a motorcycle, Awareness means your head is on a swivel. You’re scanning the road, checking mirrors, reading the body language of vehicles around you. That SUV with the driver looking at their phone? You saw it before it became a problem.
In incident response, this is the combination of Preparation (you set up your sensors, your SIEM, your alerting) and Detection (those tools actually pick up anomalies). If your observation tools are garbage, everything downstream fails. If a rider isn’t paying attention, no amount of skill saves them. If a pilot isn’t observing, they’re already dead.
Step 2 — Make Sense of What You See
This is the step Boyd considered the most important — and he was right. Observation without context is just data. Orientation is where you filter that data through your experience, your training, your cultural understanding, and your mental models to actually understand what is happening.
For riders, Assessment is where you determine the severity of the hazard. A car in the next lane isn’t automatically a threat. A car in the next lane whose wheels are turning toward your lane while the driver is looking the other way? That’s a different story. The assessment determines the response.
In cybersecurity, Analysis is where we determine whether an alert is a false positive or a genuine incident. This is the triage. This is where your experience as an analyst matters most. A junior analyst sees an alert. A senior analyst sees the same alert and knows from pattern recognition that this is the precursor to lateral movement. Same data, different orientation.
Boyd would say the analyst with the better orientation wins.
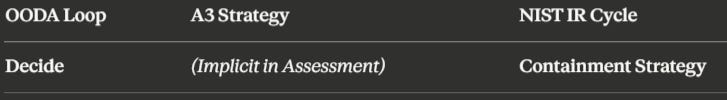
Step 3 — Commit to a Course of Action
Boyd’s Decide phase is about selecting the best response from the options your orientation generated. In a dogfight that decision might be made in milliseconds — break left, climb, engage, or disengage.
In the A3 strategy, the decision is baked into the Assessment phase. The moment you assess the severity of a hazard, your trained response kicks in. You don’t sit at a stoplight thinking about it. The training has already pre-loaded your decision tree.
In incident response, this maps to choosing your containment strategy. NIST is clear that the containment approach must match the type of attack. You don’t yank a production server offline for a phishing email. You don’t ignore a phishing email if it’s the entry point for a ransomware campaign. The decision has to be contextual, and it has to be fast.
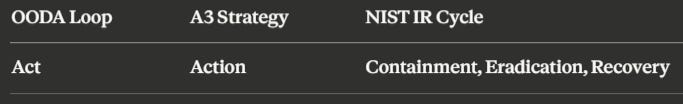
Step 4 — Execute
This is where theory meets the road, the sky, or the network. You do the thing.
The pilot executes the maneuver. The rider swerves, brakes, or accelerates out of danger. The IR team isolates the affected host, removes the malware, and begins restoring from backup.
But here’s the key — the action changes the environment. And that change demands a new loop. The pilot’s maneuver changes the relative position of every aircraft in the fight. The rider’s lane change introduces a new set of vehicles to be aware of. The containment action might trigger the attacker to pivot to a different system.
You’re back to Observe. Back to Awareness. Back to Detection.
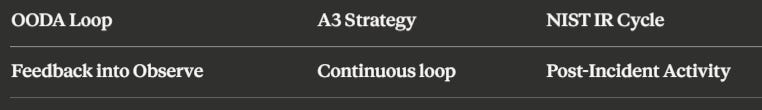
Step 5 — Learn and Feed It Back
This is where NIST is the most explicit of the three. The Post-Incident Activity phase is specifically designed to capture lessons learned and feed them back into Preparation. What worked? What broke? What playbook needs to be updated? What tool failed?
Boyd’s framework accounts for this through the implicit feedback loops in his more detailed OODA diagram — your actions generate new observations, and your orientation is constantly being updated by experience.
For riders, every close call is a lesson. Every ride is a repetition of the loop that sharpens your instincts for the next one.
Why This Matters for You
If you’re a cybersecurity professional, understanding that the NIST IR Cycle is functionally the same framework that keeps fighter pilots alive should change the way you approach your work. Speed matters. The team that can detect, analyze, and respond faster than the attacker can pivot will win the engagement.
If you’re a motorcycle rider, understanding that your A3 training is running the same cognitive loop as a combat pilot should give you both confidence and humility. Confidence that the framework works. Humility that complacency kills — because the loop only works if you keep cycling through it.
And if you’re someone who does both — rides and works in cyber — you already know this in your bones. The feeling of riding through traffic with full awareness is the same feeling as triaging a live incident with a calm, focused mind. It’s the loop in action.